History
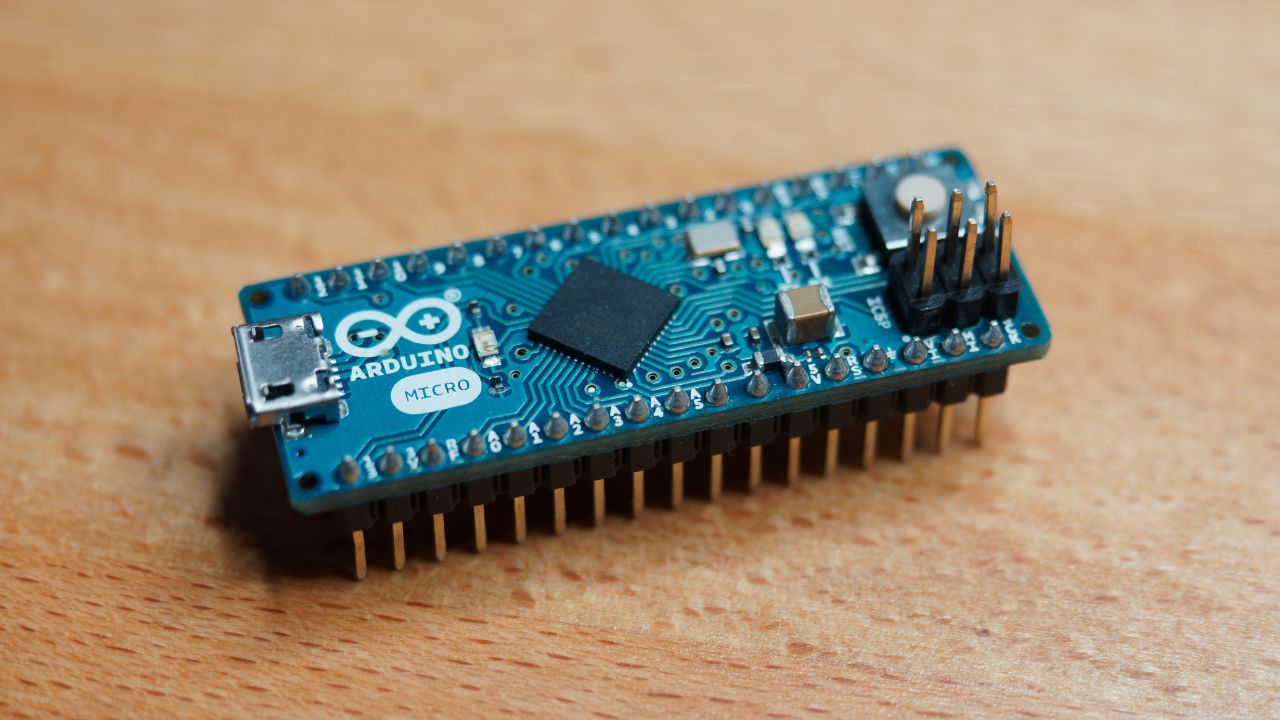
My personal history with making BadUSBs goes back to 2016, when I programmed an Arduino Micro to open a website on my computer by acting as a keyboard. I already knew about the USB Rubber Ducky and HID attacks. Still, I wanted to see if I could build one myself. Especially since I couldn't afford the famous Hak5 product as a Highschool student. Besides, being able to build a tool like this myself was a cool experience. So this is how my interest in Arduino-based hacking tools started!
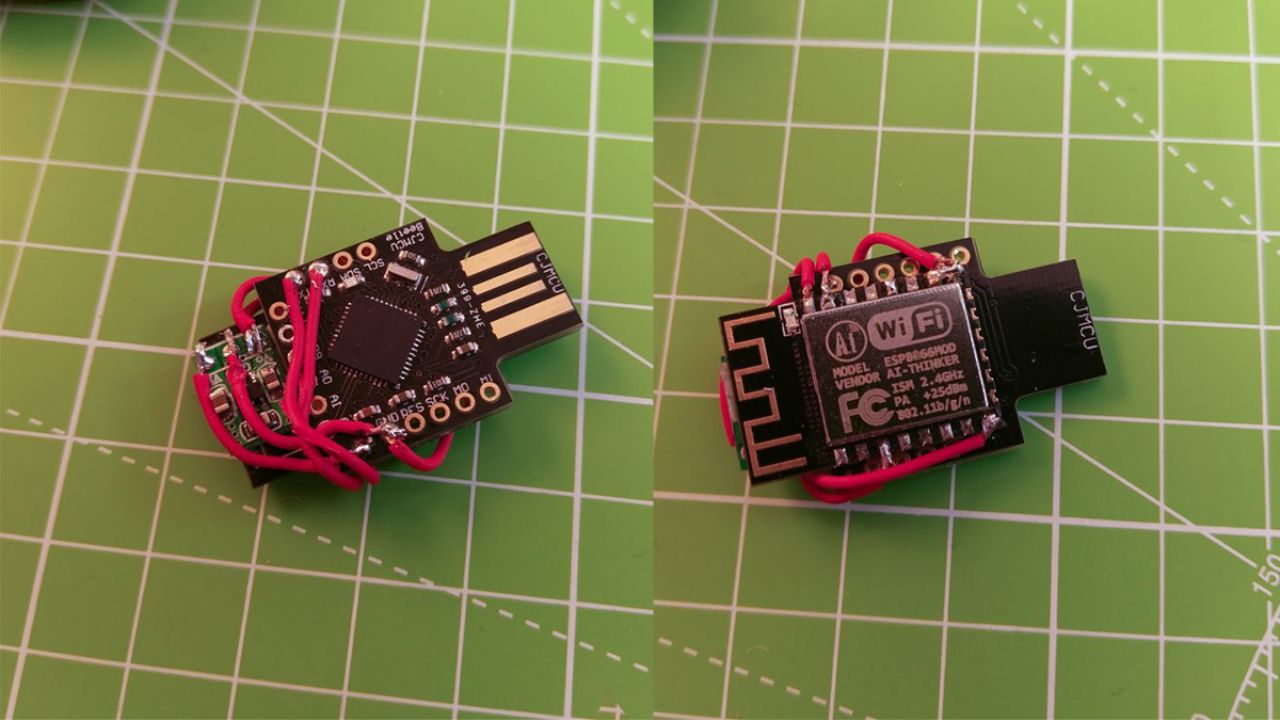
After releasing the Deauther, I wanted to build a BadUSB with the ESP8266. It had so much potential, and no one made a wireless BadUSB at that point (as far as I know). So in 2017, I made the WiFi Ducky - a DIY BadUSB that can be remote controlled via WiFi.

Around this time, I also started collaborating with Seytonic, who made the MalDuino, an Arduino-based alternative to other BadUSB products.
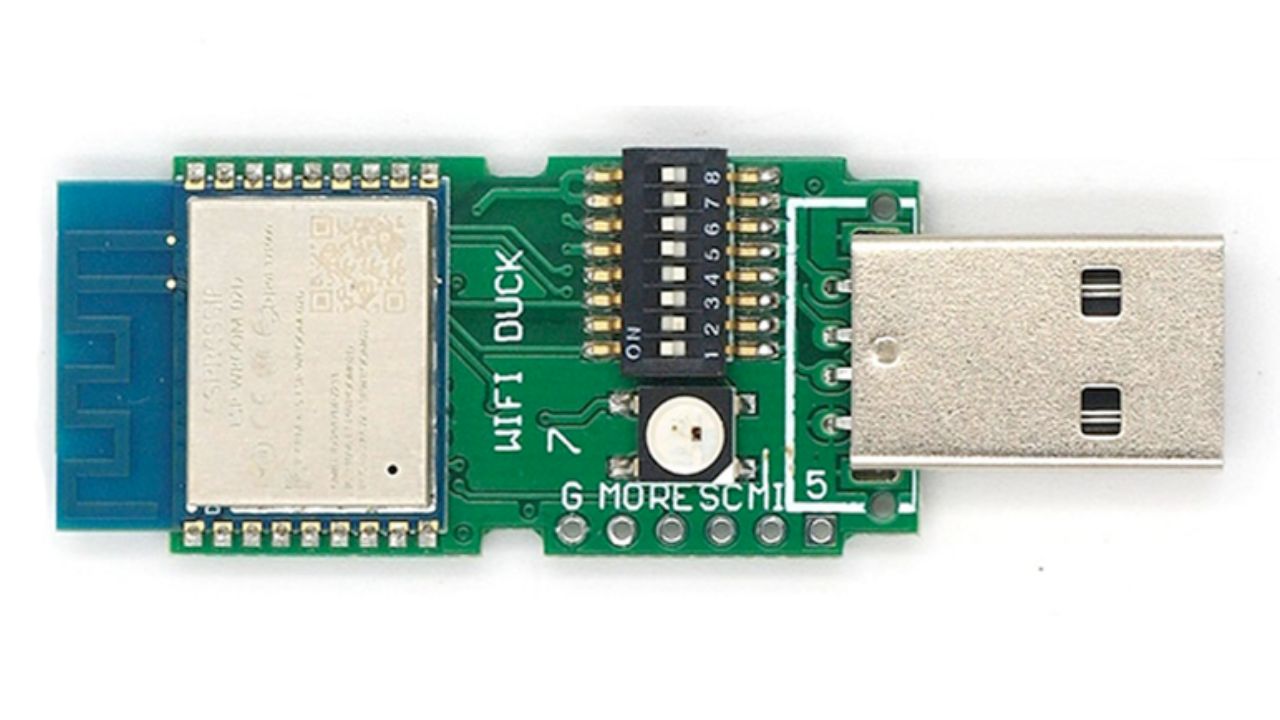
But after working on WiFi Ducky for some time, I realized I had to make more extensive changes to make developing and debugging easier. So in 2019, I released WiFi Duck, the official successor of the WiFi Ducky project. It's based on the same hardware. However, some connections slightly changed, and the firmware got a complete overhaul. As a result, it has a better user interface, is better documented, and fixed many minor bugs. It also features a lot of keyboard layouts out of the box.

Since then, I've focused more on growing my business, finishing my degree, and learning new technologies.

And now I'm continuing on the road by releasing the USB Nova - the easiest-to-use BadUSB yet; with good documentation, a colorful and user-friendly design, and cool features like the ability to act as a mass storage device. It makes it easy and fun to start exploring hacking while still being able to use it as a professional pentesting tool.
Future
I made the USB Nova and other hacking tools an Open-Source alternative to expensive proprietary solutions. It's designed to be easier to use, hackable, and encourage learning. I believe I have achieved that goal.
And I hope there will be enough demand for this product to allow for a USB-C edition and other upgrades.
Of course, I'd like to add features like OS fingerprinting and a more sophisticated scripting language to accommodate complex use cases. However, I'm just a student doing these projects in my free time. I cannot possibly compete with a million-dollar company like Hak5.
Instead, I would like to focus on education and developing new tools.
So please keep this in mind when you send me feature requests 😊.